Filter by

Blog
|
5 min read
What is Cloud Computing?
Cloud computing is not necessarily a new phenomenon. The phrase dates back to the 1990s, and concepts around mainframe s...
Read More

Blog
|
5 min read
IT Budgeting: Top Six Mistakes When Cutting IT Costs and Better Alternative...
A study in late 2019 found that 44% of organizations planned to increase IT spending in 2020. But with COVID-19 and a di...
Read More

Blog
|
3 min read
The Dark Web: What Is It and How is VC3 Making Sure Your Business Isn't On ...
You might have heard of the Dark Web from hacker films or tech thriller TV series and maybe dismissed it as something fo...
Read More
Blog
|
5 min read
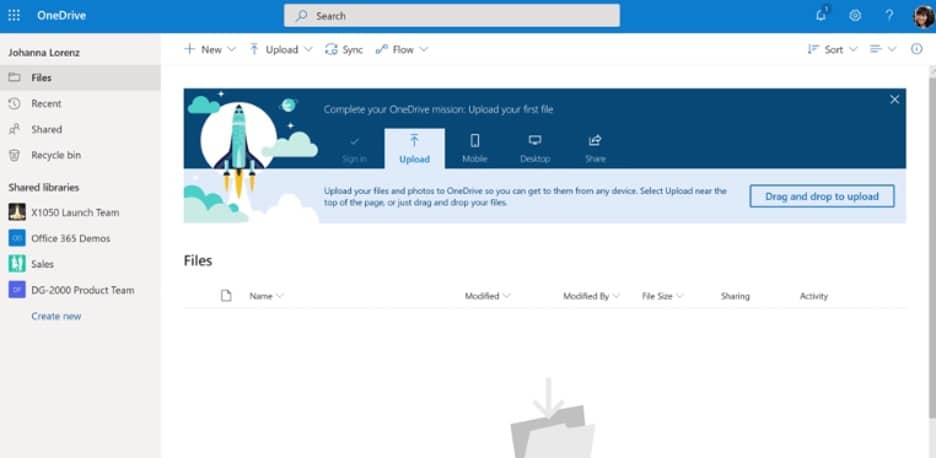
OneDrive for Business
Businesses that work with Office365, or any of the Microsoft Office suite of applications and software, will likely enco...
Read More

Blog
|
5 min read
Social Engineering Red Flags
Whenever you think of cybercrime or hacking, youll probably think about a bad actor using their technical skills to bre...
Read More
Blog
|
3 min read
Email Vigilance Critical to Combat Phishing Attacks
Start by hovering over the link in the email. When you hover your mouse over a link (but dont click on it), it brings u...
Read More
